The biggest security flaw in most WordPress sites isn’t a plugin vulnerability. It’s giving the client “Administrator” access when they only need to edit posts.
Or worse, giving an “Intern” the ability to switch_themes.
WordPress has a powerful Access Control List (ACL) system built-in. It’s called Roles & Capabilities. In this guide, we’ll move beyond the default “Editor” role and learn to architect secure permissions.
1. Concepts: Role vs capability
- Capability (Cap): A specific permission to do one thing.
- Example:
edit_posts,publish_pages,install_plugins.
- Example:
- Role: A collection of capabilities.
- Example:
Editor=edit_posts+publish_posts+manage_categories(but NOTinstall_plugins).
- Example:
Golden Rule: Always check for Capabilities, never Roles.
// ❌ WRONG
if ( current_user_can( 'administrator' ) ) { ... }
// ✅ RIGHT
if ( current_user_can( 'manage_options' ) ) { ... }2. Creating a custom role
Let’s say you have a “Store Manager” who needs to manage Products but shouldn’t touch your Theme or Plugins.
function wppoland_add_store_manager_role() {
add_role(
'store_manager',
'Store Manager',
[
'read' => true,
'edit_posts' => true,
'upload_files' => true,
'manage_woocommerce' => true, // Custom Capability
]
);
}
// Run ONLY ONCE (e.g., on theme/plugin activation)
// add_action( 'init', 'wppoland_add_store_manager_role' );Important: Roles are stored in the database (
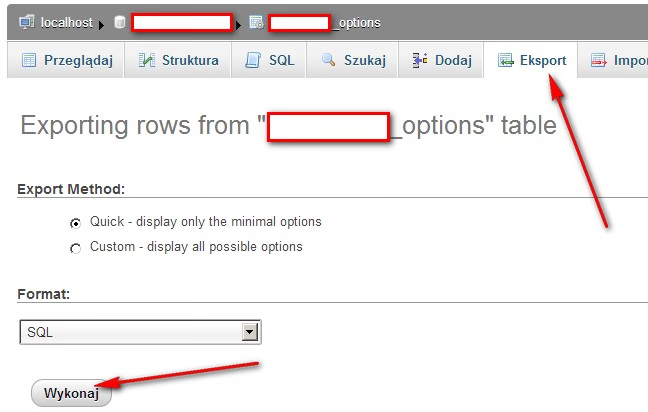
wp_options>wp_user_roles). You don’t need to runadd_roleon every page load. Run it once on activation.
3. Adding capabilities to existing roles
Sometimes you just want to let the “Editor” edit Menus (which they can’t do by default).
function wppoland_upgrade_editor() {
$role = get_role( 'editor' );
if ( $role ) {
$role->add_cap( 'edit_theme_options' ); // Allows Menu & Widget editing
}
}
// Run once4. Disaster recovery: Resetting roles
If a plugin messed up your DB or you accidentally deleted the ‘Administrator’ role (it happens!), you need a hard reset.
This script restores the default WordPress architecture.
function wppoland_reset_roles() {
if ( ! isset( $_GET['reset_roles_secret_key'] ) ) return;
require_once( ABSPATH . 'wp-admin/includes/schema.php' );
populate_roles();
echo "Roles Reset Successfully.";
exit;
}
add_action( 'init', 'wppoland_reset_roles' );5. Security best practices 2026
A. Don’t use ‘admin’ username
Brute force attacks target user ID 1 or username ‘admin’.
B. Map meta capabilities
When using Custom Post Types, don’t just use edit_posts. Map granular caps:
register_post_type( 'book', [
'capability_type' => 'book',
'map_meta_cap' => true, // Key for granular control
] );Now you can give a user edit_books without giving them edit_posts.
Summary
- Least Privilege Principle: Give users only what they need.
- Custom Roles: Better than hacking the ‘Editor’ role.
- Database: Roles live in the DB, not in code. Changes persist.
Mastering specific capabilities is the difference between a secure site and a hacked one.